What Is Zero Trust Security?

It was over a decade ago when cybersecurity industry analyst John Kindervag introduced “zero trust security” to the IT world. The idea behind the zero trust security framework was to keep user data safe from cyberattacks no matter what devices or networks were used to access the data. But although zero trust security is a great idea, it’s often misunderstood by business leaders and IT organizations alike.
Companies are struggling to take zero trust from concept to practice. Some business strategists in the C-suite are confused by the thought of zero trust security as a framework rather than a product. For decision makers and their employees, readjusting to the idea of zero trust security involves rethinking an outdated perimeter-focused cybersecurity strategy. Adopting the framework can also be daunting for some organizations because implementing zero trust security is not a one-size fits all paradigm.
Blue Mantis is unique among IT solutions providers because we are committed to infusing all our solutions with zero trust security. To help business decision makers understand how the zero trust framework enhances their organizations’ security at scale, I want to describe exactly what zero trust is—and why it is needed.
What is Zero Trust Security?
The zero trust security framework assumes that no user, device, or network connection can be trusted by default. Instead, it requires strict and continuous identification verification before granting access to data and resources.
The core tenet of zero trust security states “Trust No One.” Whether the user or asset is internal to your corporate network (in an office) or external to your network (remotely accessing). Any access to corporate data—no matter if it’s located in the cloud, on a server in a closet, or on an employee-owned tablet connected to public WiFi at a coffee shop—needs to continually be evaluated against three core principles:
- Apply Least Privilege Access – Zero trust requires IT to apply least privilege access to assets, no matter where they are located. You can also think of this as applying “just in time access,” giving just enough permission to the people who need access to the data or application that they need to do their job. For example, a company with zero trust security would not provide marketing staff members with unfettered access to financial systems. Access to HR systems in order to view employee HR records in a zero trust model if only given to authorized HR employees.
Granting least privilege access can be summarized as “just because they’re on the network doesn’t allow them to get to anything on the network.” That’s what bad actors do. They get in the network; they scan the network for any devices out there that are listening; and then they try to take advantage of vulnerabilities or misconfigurations that they can find and move laterally. Zero trust can shut that down. Within a zero trust environment, we no longer allow anyone requiring access to data or an application the ability to discovery other systems, networks, IoT devices or data outside of their privileged access capability. - Verify Identities Explicitly – As we’ve seen in many high-profile cyberattacks, identities can be forged. Millions of usernames are available to criminals on the dark web. Hackers have tools that can easily brute force a password login and even bypass multifactor authentication (MFA) in many cases to fake an authorized identity. Zero trust security requires continuous verification for establishing user identity. Imagine an employee logged in from the office on their workstation in the morning, is granted access to a system, then logs out in the evening from that workstation. So, if that same employee tries to log into the corporate email system from a coffee shop using an unknown device, a zero trust security framework looks at that login attempt with suspicion. The username and password are known, the MFA is correct, but now the user’s logging in from an unknown device.
Zero trust security asks tough questions to explicitly verify not only the user, but the device identity, too. For instance, is this device (whether it’s company-owned or personal), registered with the IT department for use by this user? Does the device have the proper anti-malware and antivirus protections sanctioned by corporate IT? Are the latest OS and application patches installed? Does the device have the latest browser updates? Based on any (or preferably all) of those criteria, zero trust can deny access. These added steps will likely trigger a call from the employee to the helpdesk, but IT decision makers should view this as a “feature” rather than “bug” of the zero trust security framework. - Assume a Breach – An organization should operate on the assumption that the bad actors are already on your network. They’re sitting there idle, watching what you’re doing, and waiting for the right time to launch the worst case scenario on your organization. To mitigate this potential disaster, zero trust requires IT teams to collect telemetry and gain deep visibility into everything. This visibility enables IT security professionals to see what is going on across networks, where the traffic on the network is originating, where it’s going, who is accessing the data, and what they’re doing with that data. By assuming your organization is already breached and having end-to-end visibility into all networks, clouds, and devices, an IT team can easily tell when bad actors are moving data offsite and determine anomalous behavior.
Is Zero Trust Security a Technology?
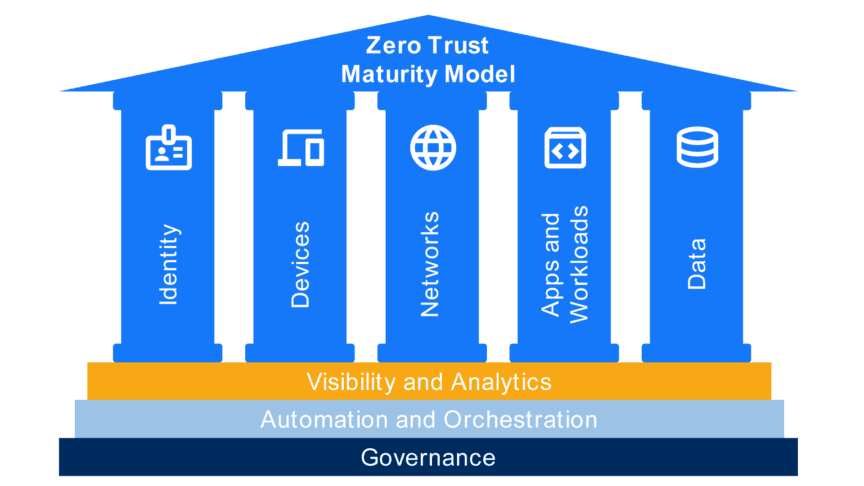
No, zero trust security is not a single technology or product that an organization can purchase. Think of it as defense in depth backed by an executable framework (based on CISA 2.0 model) and non-prescriptive abstracts like NIST 800-207. Zero trust starts with the adoption of a governance, risk and compliance program that sets the high level definition for protecting identities, devices, network and infrastructure, applications and workloads, and data. Automation and orchestration and visibility and analytics remove manual intervention and report on the zero trust environment respectively for continuous improvement.
According to the U.S. Cybersecurity and Infrastructure Security Agency (CISA), organizations can implement this strategy using the Zero Trust Security Maturity Model. It’s the same model that we use at Blue Mantis to assess a customer’s current IT security state, identify gaps and risks, prioritize actions, and track progress toward achieving zero trust security:
It is important for business leaders to understand that adhering to the zero trust security framework is a business strategy rather than a technology play. You’re right to be skeptical if a technology vendor is pitching you on a single hardware appliance for “zero trust security.” That’s because successful implementation of a zero trust framework requires multiple organizational disciplines, strategies, and technologies to come together to share context and vision before zero trust can help reduce risk and help protect an organization’s data.
Deploying IT Solutions Built on Zero Trust Security
Today’s modern workforce is cross-generational with either a significant portion of employees working either in a hybrid office or completely remote. Add to that the fact that corporate IT setups are largely cloud oriented, and you’ll get why IT leaders are so driven to balance security with productivity (while also managing costs and complexity).
By deploying IT solutions built on the zero trust framework, you can achieve these goals and benefits:
- Enhance data security and reduce cyberattack risk by eliminating unnecessary systems, apps, and network connections that can be exploited by attackers.
- Deploy, automate, and orchestrate improved security controls, monitor and respond to threats, and report on the effectiveness of your security framework.
- Enable true work from anywhere scenarios by providing your employees with the appropriate access to data and devices based on constantly-verified user identification methods.
Overwhelmed? Blue Mantis Can Help
For years, the majority of IT decision makers say that increasingly-advanced security threats make the stakes of successful data protection greater than ever. Blue Mantis builds and deploys custom IT solutions using enterprise-wide zero trust security strategies. If your business is considering a zero trust strategy, then connect with our experts. We will help you in the development, implementation, enforcement, and evolution of these powerful new security policies—and do it in a way that fits your budget.



